Related Articles
8 Best Cloud Application Security Practices
Table of Contents1 8 Best Cloud Application Security Best Practices1.1 Table of content 1.2 What is Cloud Native?1.3 Why Cloud Native?1.4 What are Cloud Native Applications?1.5 What is Cloud Native Security?1.6 Cloud Application Security Best Practices1.7 Conclusion and Summary 8 Best Cloud Application Security Best Practices Cloud Application Security Best Practices keep safe to applications. Cloud Computing […]
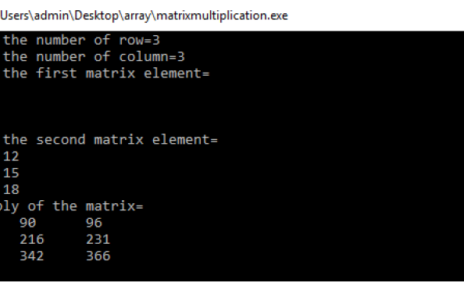
Matrix Multiplication Program in C
Table of Contents1 Matrix Multiplication Program in C1.1 Matrix Multiplication Program Algorithm1.2 Conclusion and Summary Matrix Multiplication Program in C Matrix Multiplication Program in C is an important program for the C Programming Subject. Matrix Multiplication in C Program is generally asked in AKTU Examination. In this tutorial we have explained the Matrix Multiplication in […]
Floyd Warshall Algorithm Example
Table of Contents1 Floyd Warshall Algorithm Example1.1 Frequently asked Questions1.2 What is Floyd Warshall Algorithm ?1.3 How does Floyd Warshall algorithm work ?1.4 Floyd Warshall Algorithm Example1.5 Conclusion and Summary Floyd Warshall Algorithm Example Floyd warshall algorithm example in C or Data structure is used to find the all pairs shortest path it means shortest […]